Urgent Alert: US Enterprises Hit by 3 Major Software Vulnerabilities

Anúncios
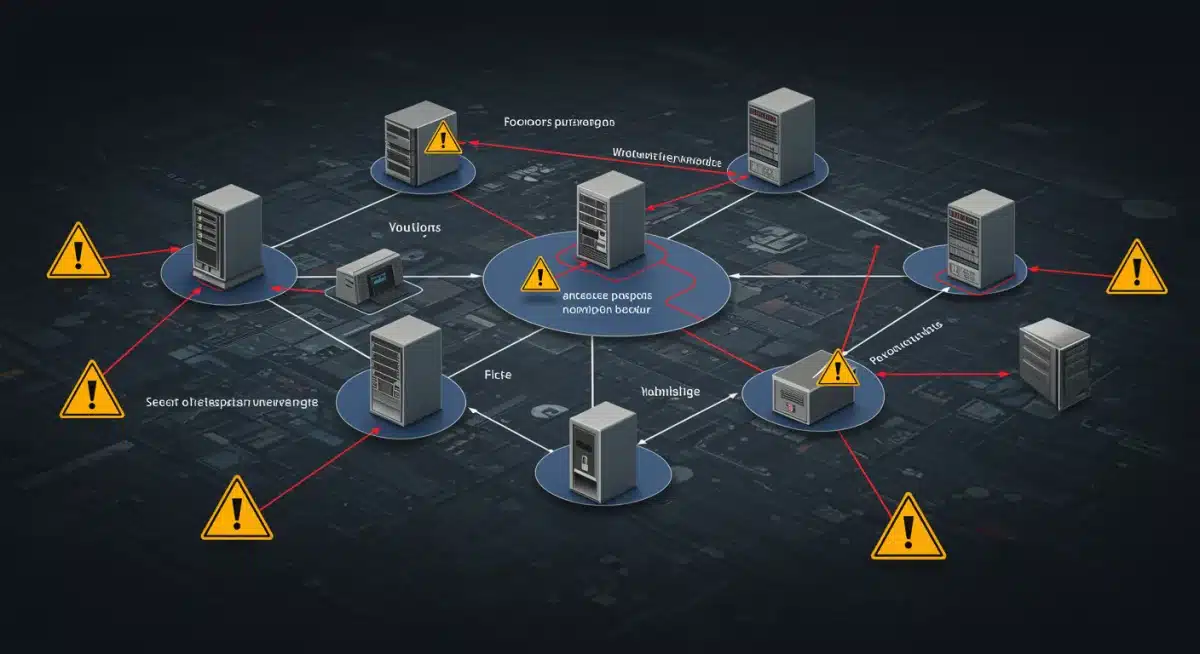
This month, US enterprises are under an urgent cybersecurity alert as sophisticated threat actors are actively exploiting three major software vulnerabilities, demanding immediate and informed responses.
Anúncios
An Urgent Alert: Latest Cybersecurity Threat Actors Exploiting 3 Major Software Vulnerabilities Across US Enterprises This Month has been issued, signaling a critical period for digital defense. Organizations nationwide are grappling with an intensified threat landscape, as malicious actors leverage newly identified weaknesses to compromise systems and data. This escalating situation demands immediate attention and proactive measures from every enterprise.
Understanding the Escalating Threat Landscape
The current cybersecurity climate is more volatile than ever, with threat actors continuously evolving their tactics. This month, US enterprises are particularly susceptible due to the active exploitation of three significant software vulnerabilities. These aren’t isolated incidents but rather part of a broader, more sophisticated campaign targeting critical infrastructure and sensitive data across various sectors.
Anúncios
The Nature of Modern Cyber Attacks
Modern cyberattacks are characterized by their stealth, persistence, and the advanced techniques used to bypass traditional security measures. Threat actors often spend weeks or months inside a network undetected, mapping systems and exfiltrating data before launching a full-scale attack. Their motivations range from financial gain and industrial espionage to geopolitical objectives, making their targets diverse and their methods adaptable.
- Advanced Persistent Threats (APTs): These groups conduct prolonged, targeted attacks to gain unauthorized access and remain undetected for extended periods.
- Ransomware as a Service (RaaS): A growing trend where sophisticated ransomware tools are leased to less skilled actors, democratizing complex attacks.
- Supply Chain Attacks: Compromising a less secure vendor to gain access to their more secure clients, creating a ripple effect of vulnerability.
The sheer volume and complexity of these threats necessitate a robust and adaptive defense strategy. Enterprises must move beyond reactive measures and embrace a proactive security posture to effectively counter these evolving dangers.
Vulnerability 1: Critical Zero-Day in Cloud Management Platform
The first major vulnerability under active exploitation is a critical zero-day flaw discovered in a widely used cloud management platform. This particular flaw allows unauthenticated remote code execution, granting attackers full control over affected systems without needing legitimate credentials. The impact on US enterprises leveraging this platform for their cloud operations is severe, ranging from data breaches to complete system compromise.
Impact and Exploitation Details
Threat actors are quickly weaponizing this zero-day, using automated scripts to scan for vulnerable instances across the internet. Once identified, they deploy sophisticated payloads to establish persistent access, exfiltrate sensitive data, and often set the stage for further lateral movement within the compromised network. The speed at which this vulnerability has been exploited underscores the urgency for immediate patching and mitigation.
- Data Exfiltration: Attackers can steal vast amounts of confidential enterprise data, including intellectual property and customer information.
- System Takeover: Full control over cloud resources, leading to service disruption, data manipulation, or even destruction.
- Lateral Movement: Using the compromised cloud platform as a stepping stone to access other internal enterprise systems.
Organizations must prioritize patching this vulnerability immediately. For those unable to patch, implementing strict network segmentation and monitoring for suspicious activity on cloud-connected systems is paramount to minimize exposure.
Vulnerability 2: Exploitation in Enterprise Resource Planning (ERP) Software
The second critical vulnerability being actively exploited targets a widely deployed Enterprise Resource Planning (ERP) software suite. This flaw specifically resides within the system’s authentication module, allowing attackers to bypass login protections and gain unauthorized access to sensitive business data and processes. Given the central role of ERP systems in modern enterprises, this exploitation poses a significant risk to operational integrity and financial stability.
Threat Actor Motivations and Tactics
Threat actors exploiting this ERP vulnerability are primarily motivated by financial gain and competitive advantage. By gaining access to ERP systems, they can manipulate financial records, steal customer databases, disrupt supply chains, or even introduce fraudulent transactions. Their tactics often involve phishing campaigns to deliver initial access, followed by sophisticated privilege escalation techniques to fully compromise the ERP environment.
The compromised ERP systems become a treasure trove for malicious actors, enabling them to extract highly sensitive information that can be sold on dark web markets or used for targeted blackmail. Furthermore, the disruption caused by tampering with ERP data can lead to severe operational paralysis for affected companies.

Enterprises using the affected ERP software must conduct thorough security audits, apply vendor-recommended patches, and implement multi-factor authentication (MFA) across all ERP accounts. Proactive monitoring for unusual login patterns or data access attempts is also crucial to detect and respond to potential compromises swiftly.
Vulnerability 3: Remote Code Execution in Collaboration Tool
The third major vulnerability under active exploitation affects a popular enterprise collaboration tool, specifically a remote code execution (RCE) flaw. This vulnerability allows attackers to execute arbitrary code on systems running the affected software, turning a tool designed for team productivity into a potent weapon for network intrusion. The widespread adoption of these tools across US enterprises makes this a particularly concerning threat, as it can provide a direct pathway into corporate networks.
How the Exploitation Unfolds
The exploitation of this RCE vulnerability typically begins with threat actors sending specially crafted messages or files through the collaboration platform. When an unsuspecting user opens or interacts with this malicious content, the RCE flaw is triggered, allowing the attacker to execute commands on the user’s machine. From there, attackers can install malware, establish backdoors, or attempt to move laterally to other systems within the enterprise network.
- Initial Access: Malicious files or links shared through the collaboration tool act as the initial vector.
- Malware Deployment: Attackers install ransomware, spyware, or other malicious software on the compromised endpoint.
- Privilege Escalation: Exploiting local system vulnerabilities to gain higher-level access within the network.
The collaborative nature of these tools, which encourages sharing and interaction, inadvertently creates an ideal environment for such exploits to spread rapidly. Enterprises must educate their employees about the risks, enforce strict content filtering, and ensure all collaboration software is updated to the latest secure versions.
Proactive Measures and Mitigation Strategies
In response to these urgent threats, US enterprises must adopt a multi-layered approach to cybersecurity. Relying solely on perimeter defenses is no longer sufficient; a comprehensive strategy encompassing technology, processes, and people is essential for resilience against sophisticated threat actors.
Immediate Action Steps
Addressing these vulnerabilities requires swift and decisive action. Organizations should prioritize vulnerability scanning, patch management, and incident response planning to minimize their attack surface and improve their ability to react to ongoing threats. Regular security audits and penetration testing can also identify weaknesses before they are exploited by malicious actors.
Furthermore, investing in advanced threat detection systems, such as Endpoint Detection and Response (EDR) and Security Information and Event Management (SIEM) solutions, can provide early warnings of suspicious activities. These tools help security teams identify and neutralize threats before they can cause significant damage, offering a critical layer of defense.
Building a Resilient Cybersecurity Posture
Beyond immediate remediation, the current threat landscape underscores the need for enterprises to build a fundamentally resilient cybersecurity posture. This involves fostering a culture of security awareness, implementing robust access controls, and developing comprehensive incident response plans that are regularly tested and updated. A strong security posture is not a one-time project but an ongoing commitment to adaptation and vigilance.
The Role of Employee Training and Awareness
Employees are often the first line of defense, and their awareness of cybersecurity best practices is paramount. Regular training on phishing recognition, secure browsing habits, and reporting suspicious activities can significantly reduce the likelihood of successful social engineering attacks. A well-informed workforce is a powerful asset in the fight against cyber threats.
- Phishing Simulations: Regularly test employees with simulated phishing emails to gauge their susceptibility and reinforce training.
- Secure Password Policies: Enforce strong, unique passwords and the use of password managers.
- Reporting Protocols: Establish clear procedures for employees to report any suspicious activity or potential security incidents.
By empowering employees with the knowledge and tools to identify and avoid cyber threats, enterprises can significantly enhance their overall security posture and reduce the risk of falling victim to sophisticated attacks.
| Key Threat | Brief Description |
|---|---|
| Cloud Platform Zero-Day | Critical vulnerability allowing remote code execution, leading to full system control. |
| ERP Software Flaw | Authentication bypass in ERP systems, granting unauthorized access to sensitive business data. |
| Collaboration Tool RCE | Remote Code Execution in popular collaboration software, enabling malware deployment. |
| Proactive Defense | Immediate patching, employee training, and advanced threat detection are crucial. |
Frequently Asked Questions About Cybersecurity Vulnerabilities
US enterprises should immediately identify if they use the affected software, apply all available patches, and isolate vulnerable systems if patching isn’t possible. Enhance network monitoring for suspicious activity and review incident response plans.
Zero-day vulnerabilities are flaws unknown to the vendor, meaning no patch exists when they are discovered and exploited. This makes them particularly dangerous as organizations have no immediate defense, unlike known flaws with available patches.
Employee training is crucial. Many exploits, especially those leveraging collaboration tools, rely on social engineering. Educated employees can recognize phishing attempts and suspicious links, acting as a vital human firewall against these sophisticated attacks.
Yes, SMBs are increasingly targeted. While they may not have the same data volume as larger corporations, they often have weaker defenses, making them attractive targets for initial access to a supply chain attack or for direct financial gain through ransomware.
Long-term strategies include implementing a robust patch management program, investing in advanced threat detection, maintaining regular security audits, and fostering a culture of cybersecurity awareness throughout the organization. Continuous adaptation to new threats is essential.
Conclusion
The current wave of cybersecurity threats, marked by the active exploitation of three major software vulnerabilities across US enterprises, serves as a stark reminder of the persistent and evolving dangers in the digital realm. Immediate action, including comprehensive patching and enhanced monitoring, is paramount to mitigate the risks posed by these sophisticated threat actors. Beyond reactive measures, fostering a proactive and resilient cybersecurity posture through continuous employee education, robust technological safeguards, and adaptive incident response planning is essential for safeguarding organizational integrity and data in the face of an ever-changing threat landscape.